Introduction
Ubuntu Linux uses groups to help you manage users, set permissions on those users, and even monitor how much time they are spending in front of the PC. .
Normally Linux computers have two user accounts—your own user account, and the root account, which is the super user that can access everything on the PC, make system changes, and administer other users.
Ubuntu works a little differently, though—you can’t login directly as root by default, and you use the sudo command to switch to root-level access when you need to make a change.
Accounts on a Unix system
Root account: This is also called superuser and would have complete and unfettered control of the system. A superuser can run any commands without any restriction. This user should be assumed as a system administrator.
System accounts: System accounts are those needed for the operation of system-specific components for example mail accounts and the sshd accounts. These accounts are usually needed for some specific function on your system, and any modifications to them could adversely affect the system.
User accounts: User accounts provide interactive access to the system for users and groups of users. General users are typically assigned to these accounts and usually have limited access to critical system files and directories.
Unix Users and Groups
User account information is stored in several ASCII configuration files:
- etc/passwd – User accounts.
- etc/shadow – Encoded passwords and password settings. As we’ll see, the name and location of this file varies.
- etc/group – Group definitions and memberships.
- etc/gshadow – Group passwords and administrators (Linux only).
The Password File – etc/passwd
The file etc/passwd is the system’s master list of information about users, and every user account has an entry within it. Each entry in the password file is a single line having the following form:
username:x:UID:GID:user information:home-directory:login-shell
The meanings of the fields are as follows:
- Username –The username assigned to the user
- X – Traditionally, the second field in each password file entry holds the user’s encoded password.
- UID -The user identification number. Each distinct human user should have a unique UID. Conventionally, UIDs below 100 are used for system accounts (Linux now uses 500 as the cutoff)
- GID The user’s primary group membership. This number is usually the identification number assigned to a group in the file etc/group
- user information Conventionally contains the user’s full name and, possibly, other job-related information.
- home directory The user’s home directory. When the user logs in, this is her initial working directory, and it is also the location where she will store her personal files.
- login shell The program used as the command interpreter for this user. Whenever the user logs in, this program is automatically started. This is usually one of bin/sh (Bourne shell), bin/csh (C shell), or /bin/ksh (Korn shell)
The Shadow Password File - etc/shadow
Most Unix operating systems support a shadow password file: an additional useraccount database file designed to store the encrypted passwords. On most systems, the password file must be world-readable in order for any command or service that translates usernames to/from UIDs to function properly. Linux etc/shadow
jsag:$1$CzzxUSse$bKJL9wAns39vlxQlBZ8wd/:13744:0:99999:7:::
The meanings of the fields are as follows:
- First field is username
- Second is the salted hash or account status
- NP or ! or null for blank password, LK or * for locked/disabled account, !! for account with expired password
- Third is days since last password change Measured from epoch (midnight UTC 1/1/1970)
- Fourth is days until password is eligible to be changed
- Fifth is days before change is required
- Sixth is days before expiration to warn
- Seventh is days before account expires
- Eighth is days since epoch when account expires
- Ninth is unused/reserved
The Group File - etc/group
Unix groups are a mechanism provided to enable arbitrary collections of users to share files and other system resources. As such, they provide one of the cornerstones of system security.
Groups may be defined in two ways:
Implicitly, by GID; whenever a new GID appears in the fourth field of the password file, a new group is defined.
Explicitly, by name and GID, via an entry in the file etc/group.
The best administrative practice is to define all groups explicitly in the etc/group file
Each entry in etc/group consists of a single line with the following form:
name:*:GID:additional-users
The meanings of these fields are as follows:
- Name A name identifying the group. Names are often restricted to eight characters.
- * or ! The second field is the traditional group password field, but it now holds somesort of placeholder character.
- GID This is the group’s identification number. User groups generally start numbering at 100.
- additional-users This field holds a list of users (and, on some systems, groups) who are members of the group, in addition to those users belonging to the group by virtue of etc/passwd (who need not be listed). Names must be separated by commas (but nospaces may appear within the list).
Adding a New User Account
Adding a new user to the system involves the following tasks:
- Assign the user a username, a user ID number, and a primary group, and decide which other groups she should be a member of (if any). Enter this data into the system user account configuration files.
- Assign a password to the new account.
- Create a home directory for the user.
- Place initialization files in the user’s home directory
Set other user account parameters appropriate for your system (possibly including password aging, account expiration date, resource limits, and system privileges). - Add the user to any other facilities in use as appropriate (e.g., the disk quota system, mail system, and printing system).
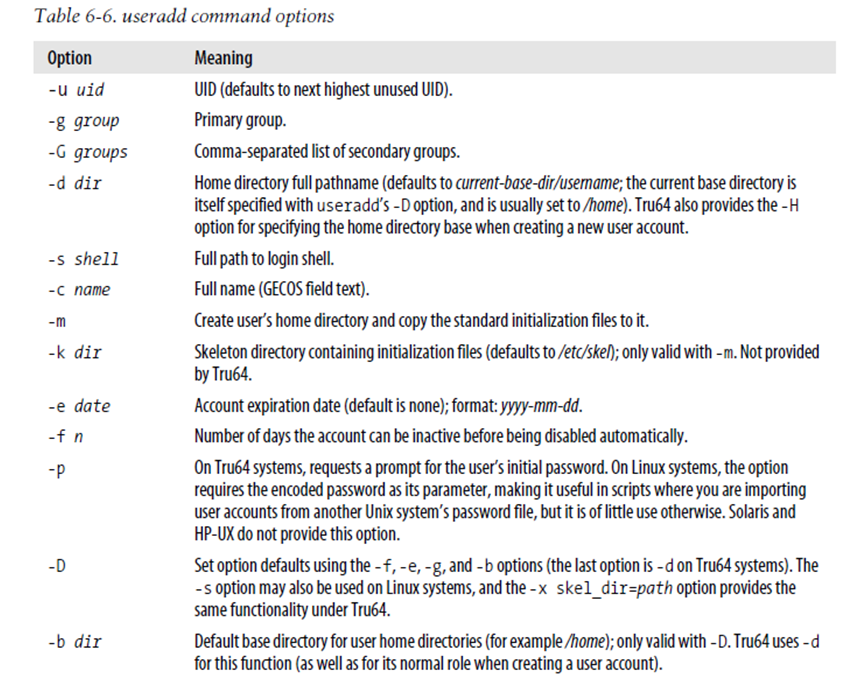
Sudo useradd –d /home/masenostdnt –m jsagimo
Sudo useradd –d /home/masenostdnt –m –G sambashare,cdrom jsagimo
Changing the shell for a user and adding comment
Sudo usermod -s /bin/bash -c “ BBIT student” jsagimo
Adding a Group – Sudo groupadd –g 10000 Hrusers
Sudo groupmod –g 15000 Hrusers